This chapter describes authentication, authorization, and accounting (AAA) used to monitor and control network access on the 7705 SAR. Network security is based on a multi-step process. The first step, authentication, validates a user’s name and password. The second step is authorization, which allows the user to access and execute commands at various command levels based on profiles assigned to the user.
The third step, accounting, keeps track of the activity of a user who has accessed the network. The type of accounting information recorded can include a history of the commands executed, the amount of time spent in the session, the services accessed, and the data transfer size during the session. The accounting data can then be used to analyze trends, and also for billing and auditing purposes.
You can configure the 7705 SAR to use local, Remote Authentication Dial In User Service (RADIUS), or Terminal Access Controller Access Control System Plus (TACACS+) security to validate users who attempt to access the router by console, Telnet, SSH, SFTP, SCP, or FTP. You can select the authentication order that determines the authentication method to try first, second, and third.
The 7705 SAR supports the following security features:
RADIUS can be used for authentication, authorization, and accounting
TACACS+ can be used for authentication, authorization, and accounting
local security can be implemented for authentication and authorization
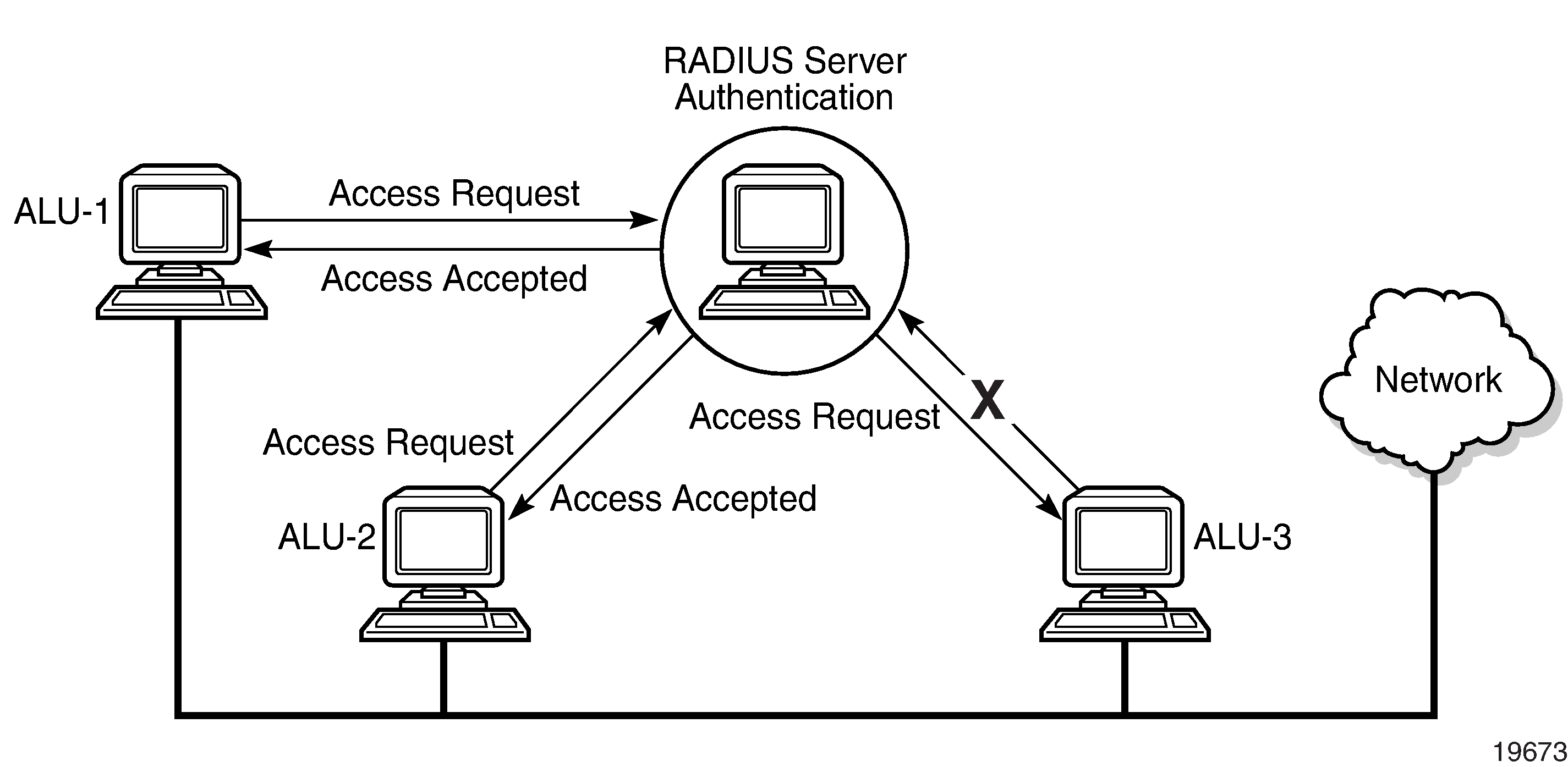
Figure: RADIUS Requests and Responses depicts end-user access requests sent to a RADIUS server. After validating the usernames and passwords, the RADIUS server returns an access accept message to the users on ALU-1 and ALU-2. The username and password from ALU-3 could not be authenticated; therefore, access was denied.