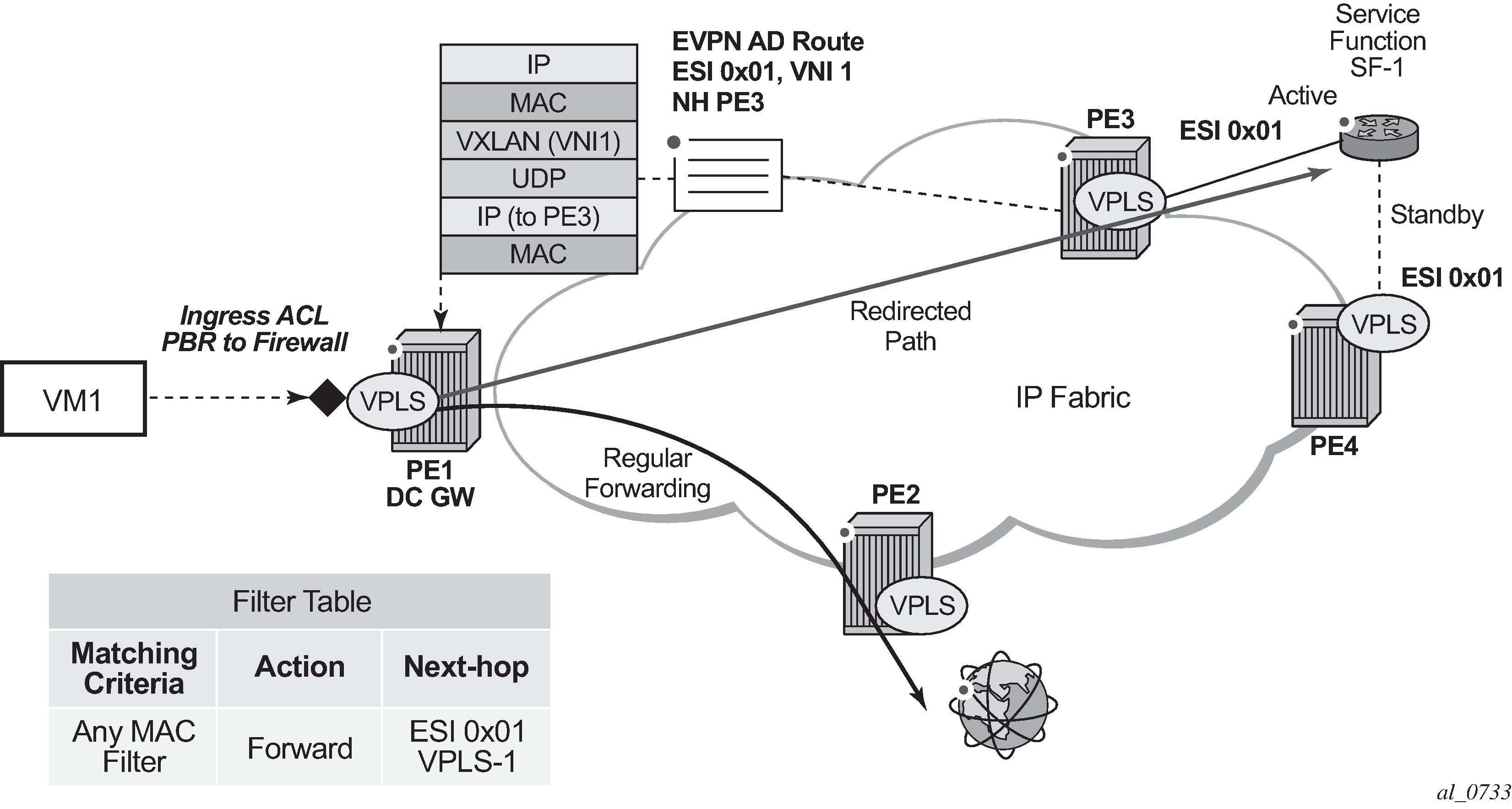
Figure 1 shows the 7750 SR, 7450 ESS, and 7950 XRS Service Chaining integration with the Nuage VSP on VPLS services. In this example, the DC gateway, PE1, is connected to an L2-DOMAIN that exists in the DC and must redirect the traffic to the Service Function SF-1. The regular Layer 2 forwarding procedures would have taken the packets to PE2, as opposed to SF-1.
An operator must configure a PBF match/action filter policy entry in an IPv4 or MAC ingress access or network filter deployed on a VPLS interface using CLI/SNMP/NETCONF management interfaces. The PBF target is the first service function in the chain (SF-1) that is identified by an ESI.
In the example shown in Figure 1, the PBF filter redirects the matching packets to ESI 0x01 in VPLS-1.
Figure 1 represents ESI as ‟0x01” for simplicity; in reality, the ESI is a 10-byte number.
As soon as the redirection target is configured and associated with the vport connected to SF-1, the Nuage VSC (Virtual Services Controller, or the remote PE3 in the example) advertises the location of SF-1 via an Auto-Discovery Ethernet Tag route (route type 1) per-EVI. In this AD route, the ESI associated with SF-1 (ESI 0x01) is advertised along with the VTEP (PE3's IP) and VNI (VNI-1) identifying the vport where SF-1 is connected. PE1 sends all the frames matching the ingress filter to PE3's VTEP and VNI-1.
When packets get to PE3, VNI-1 (the VNI advertised in the AD route) indicate that a cut-through switching operation is needed to deliver the packets straight to the SF-1 vport, without the need for a regular MAC lookup.
The following filter configuration shows an example of PBF rule redirecting all the frames to an ESI.
A:PE1>config>filter>mac-filter# info
----------------------------------------------
default-action forward
entry 10 create
action
forward esi ff:00:00:00:00:00:00:00:00:01 service-id 301
exit
exit
When the filter is properly applied to the VPLS service (VPLS-301 in this example), it shows 'Active' in the following show commands as long as the Auto-Discovery route for the ESI is received and imported.
A:PE1# show filter mac 1
===============================================================================
Mac Filter
===============================================================================
Filter Id : 1 Applied : Yes
Scope : Template Def. Action : Forward
Entries : 1 Type : normal
Description : (Not Specified)
-------------------------------------------------------------------------------
Filter Match Criteria : Mac
-------------------------------------------------------------------------------
Entry : 10 FrameType : Ethernet
Description : (Not Specified)
Log Id : n/a
Src Mac : Undefined
Dest Mac : Undefined
Dot1p : Undefined Ethertype : Undefined
DSAP : Undefined SSAP : Undefined
Snap-pid : Undefined ESnap-oui-zero : Undefined
Match action: Forward (ESI) Active
ESI : ff:00:00:00:00:00:00:00:00:01
Svc Id : 301
PBR Down Act: Forward (entry-default)
Ing. Matches: 3 pkts
Egr. Matches: 0 pkts
===============================================================================
A:PE1# show service id 301 es-pbr
===============================================================================
L2 ES PBR
===============================================================================
ESI Users Status
VTEP:VNI
-------------------------------------------------------------------------------
ff:00:00:00:00:00:00:00:00:01 1 Active
192.0.2.72:7272
-------------------------------------------------------------------------------
Number of entries : 1
-------------------------------------------------------------------------------
===============================================================================
Details of the received AD route that resolves the filter forwarding are shown in the following show router bgp routes command.
A:PE1# show router bgp routes evpn auto-
disc esi ff:00:00:00:00:00:00:00:00:01
===============================================================================
BGP Router ID:192.0.2.71 AS:64500 Local AS:64500
===============================================================================
Legend -
Status codes : u - used, s - suppressed, h - history, d - decayed, * - valid
l - leaked, x - stale, > - best, b - backup
Origin codes : i - IGP, e - EGP, ? - incomplete
===============================================================================
BGP EVPN Auto-Disc Routes
===============================================================================
Flag Route Dist. ESI NextHop
Tag Label
-------------------------------------------------------------------------------
u*>i 192.0.2.72:100 ff:00:00:00:00:00:00:00:00:01 192.0.2.72
0 VNI 7272
-------------------------------------------------------------------------------
Routes : 1
=============================================================
This AD route, when used for PBF redirection, is added to the list of EVPN-VXLAN bindings for the VPLS service and shown as 'L2 PBR' type:
A:PE1# show service id 301 vxlan
===============================================================================
VPLS VXLAN, Ingress VXLAN Network Id: 301
===============================================================================
Egress VTEP, VNI
===============================================================================
VTEP Address Egress VNI Num. MACs Mcast Oper State L2 PBR
-------------------------------------------------------------------------------
192.0.2.69 301 1 Yes Up No
192.0.2.72 301 1 Yes Up No
192.0.2.72 7272 0 No Up Yes
-------------------------------------------------------------------------------
Number of Egress VTEP, VNI : 3
-------------------------------------------------------------------------------
===============================================================================
If the AD route is withdrawn, the binding disappears and the filter is inactive again. The user can control whether the matching packets are dropped or forwarded if the PBF target cannot be resolved by BGP.
ES-based PBF filters can be applied only on services with the default bgp (vxlan) instance (instance 1).