VPLS services support proxy-ARP (Address Resolution Protocol) and proxy-ND (Neighbor Discovery) functions that can be enabled or disabled independently per service. When enabled (proxy-ARP/proxy-ND no shutdown), the system populates the corresponding proxy-ARP/proxy-ND table with IP--MAC entries learned from the following sources:
EVPN-received IP-MAC entries
User-configured static IP-MAC entries
Snooped dynamic IP-MAC entries (learned from ARP/GARP/NA messages received on local SAPs/SDP bindings)
In addition, any ingress ARP or ND frame on a SAP or SDP binding is intercepted and processed. ARP requests and Neighbor Solicitations are answered by the system if the requested IP address is present in the proxy table.
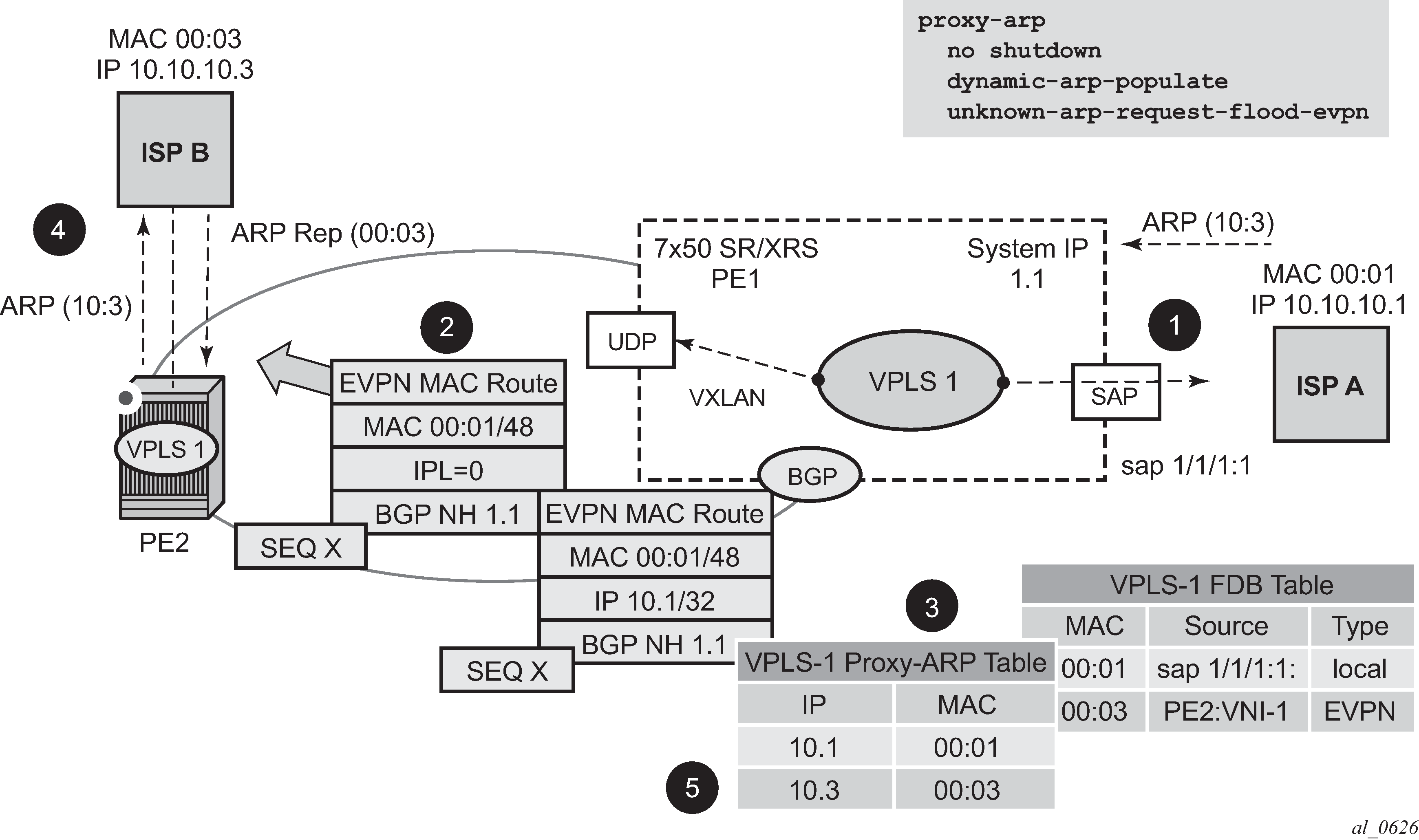
Figure: Proxy-ARP example usage in an EVPN network shows an example of how proxy-ARP is used in an EVPN network. Proxy-ND would work in a similar way. The MAC address notation in the diagram is shortened for readability.
PE1 is configured as follows:
*A:PE1>config>service>vpls# info
----------------------------------------------
vxlan instance 1 vni 600 create
exit
bgp
route-distinguisher 192.0.2.71:600
route-target export target:64500:600 import target:64500:600
exit
bgp-evpn
vxlan bgp 1 vxlan-instance 1
no shutdown
exit
exit
proxy-arp
age-time 600
send-refresh 200
dup-detect window 3 num-moves 3 hold-down max anti-spoof-
mac 00:ca:ca:ca:ca:ca
dynamic-arp-populate
no shutdown
exit
sap 1/1/1:600 create
exit
no shutdown
----------------------------------------------
Figure: Proxy-ARP example usage in an EVPN network shows the following steps, assuming proxy-ARP is no shutdown on PE1 and PE2, and the tables are empty:
ISP-A sends ARP-request for (10.10.)10.3.
PE1 learns the MAC 00:01 in the FDB as usual and advertises it in EVPN without any IP. Optionally, the MAC can be configured as a CStatic mac, in which case it is advertised as protected. If the MAC is learned on a SAP or SDP binding where auto-learn-mac-protect is enabled, the MAC is also advertised as protected.
The ARP-request is sent to the CPM where:
An ARP entry (IP 10.1'MAC 00:01) is populated into the proxy-ARP table.
EVPN advertises MAC 00:01 and IP 10.1 in EVPN with the same SEQ number and Protected bit as the previous route-type 2 for MAC 00:01.
A GARP is also issued to other SAPs/SDP bindings (assuming they are not in the same split horizon group as the source). If garp-flood-evpn is enabled, the GARP message is also sent to the EVPN network.
The original ARP-request can still be flooded to the EVPN or not based on the unknown-arp-request-flood-evpn command.
Assuming PE1 was configured with unknown-arp-request-flood-evpn, the ARP-request is flooded to PE2 and delivered to ISP-B. ISP-B replies with its MAC in the ARP-reply. The ARP-reply is finally delivered to ISP-A.
PE2 learns MAC 00:01 in the FDB and the entry 10.1'00:01 in the proxy-ARP table, based on the EVPN advertisements.
When ISP-B replies with its MAC in the ARP-reply:
MAC 00:03 is learned in FDB at PE2 and advertised in EVPN.
MAC 00:03 and IP 10.3 are learned in the proxy-ARP table and advertised in EVPN with the same SEQ number as the previous MAC route.
ARP-reply is unicasted to MAC 00:01.
EVPN advertisements are used to populate PE1's FDB (MAC 00:03) and proxy-ARP (IP 10.3—>MAC 00:03) tables as mentioned in 5.
From this point onward, the PEs reply to any ARP-request for 00:01 or 00:03, without the need for flooding the message in the EVPN network. By replying to known ARP-requests / Neighbor Solicitations, the PEs help to significantly reduce the flooding in the network.
Use the following commands to customize proxy-ARP/proxy-ND behavior:
dynamic-arp-populate and dynamic-nd-populate
Enables the addition of dynamic entries to the proxy-ARP or proxy-ND table (disabled by default). When executed, the system populates proxy-ARP/proxy-ND entries from snooped GARP/ARP/NA messages on SAPs/SDP bindings in addition to the entries coming from EVPN (if EVPN is enabled). These entries are shown as dynamic.
static <IPv4-address> <mac-address> and static <IPv4-address> <mac-address> and static <ipv6-address> <mac-address> {host | router}
Configures static entries to be added to the table.
Note: A static IP-MAC entry requires the addition of the MAC address to the FDB as either learned or CStatic (conditional static mac) to become active (Status —> active).age-time <60 to 86400> (seconds)
Specifies the aging timer per proxy-ARP/proxy-ND entry. When the aging expires, the entry is flushed. The age is reset when a new ARP/GARP/NA for the same IP MAC is received.
send-refresh <120 to 86400> (seconds)
If enabled, the system sends ARP-request/Neighbor Solicitation messages at the configured time, so that the owner of the IP can reply and therefore refresh its IP MAC (proxy-ARP entry) and MAC (FDB entry).
table-size [1 to 16384]
Enables the user to limit the number of entries learned on a specified service. By default, the table-size limit is 250.
The unknown ARP-requests, NS, or the unsolicited GARPs and NA messages can be configured to be flooded or not in an EVPN network with the following commands:
proxy-arp [no] unknown-arp-request-flood-evpn
proxy-arp [no] garp-flood-evpn
proxy-nd [no] unknown-ns-flood-evpn
proxy-nd [no] host-unsolicited-na-flood-evpn
proxy-nd [no] router-unsolicited-na-flood-evpn
dup-detect [anti-spoof-mac <mac-address>] window <minutes> num-moves <count> hold-down <minutes | max>
Enables a mechanism that detects duplicate IPs and ARP/ND spoofing attacks. The working of the dup-detect command can be summarized as follows:
Attempts (relevant to dynamic and EVPN entry types) to add the same IP (different MAC) are monitored for <window> minutes and when <count> is reached within that window, the proxy-ARP/proxy-ND entry for the IP is suspected and marked as duplicate. An alarm is also triggered.
The condition is cleared when hold-down time expires (max does not expire) or a clear command is issued.
If the anti-spoof-mac is configured, the proxy-ARP/proxy-ND offending entry's MAC is replaced by this <mac-address> and advertised in an unsolicited GARP/NA for local SAP or SDP bindings and in EVPN to remote PEs.
This mechanism assumes that the same anti-spoof-mac is configured in all the PEs for the same service and that traffic with destination anti-spoof-mac received on SAPs/SDP bindings are dropped. An ingress MAC filter has to be configured to drop traffic to the anti-spoof-mac.
Table: Proxy-arp entry combinations shows the combinations that produce a Status = Active proxy-arp entry in the table. The system replies to proxy-ARP requests for active entries. Any other combination results in a Status = inActv entry. If the service is not active, the proxy-arp entries are not active either, regardless of the FDB entries
| Proxy-arp entry type | FDB entry type (for the same MAC) |
|---|---|
Dynamic |
learned |
Static |
learned |
Dynamic |
CStatic/Static |
Static |
CStatic/Static |
EVPN |
EVPN, learned/CStatic/Static with matching ESI |
Duplicate |
— |
When proxy-ARP/proxy-ND is enabled on services with all-active multihomed Ethernet Segments, a proxy-arp entry type evpn may be associated with learned/CStatic/Static FDB entries (because for example, the CE can send traffic for the same MAC to all the multihomed PEs in the ES). If this is the case, the entry is active if the ESI of the EVPN route and the FDB entry match, or inactive otherwise, as per Table: Proxy-arp entry combinations.