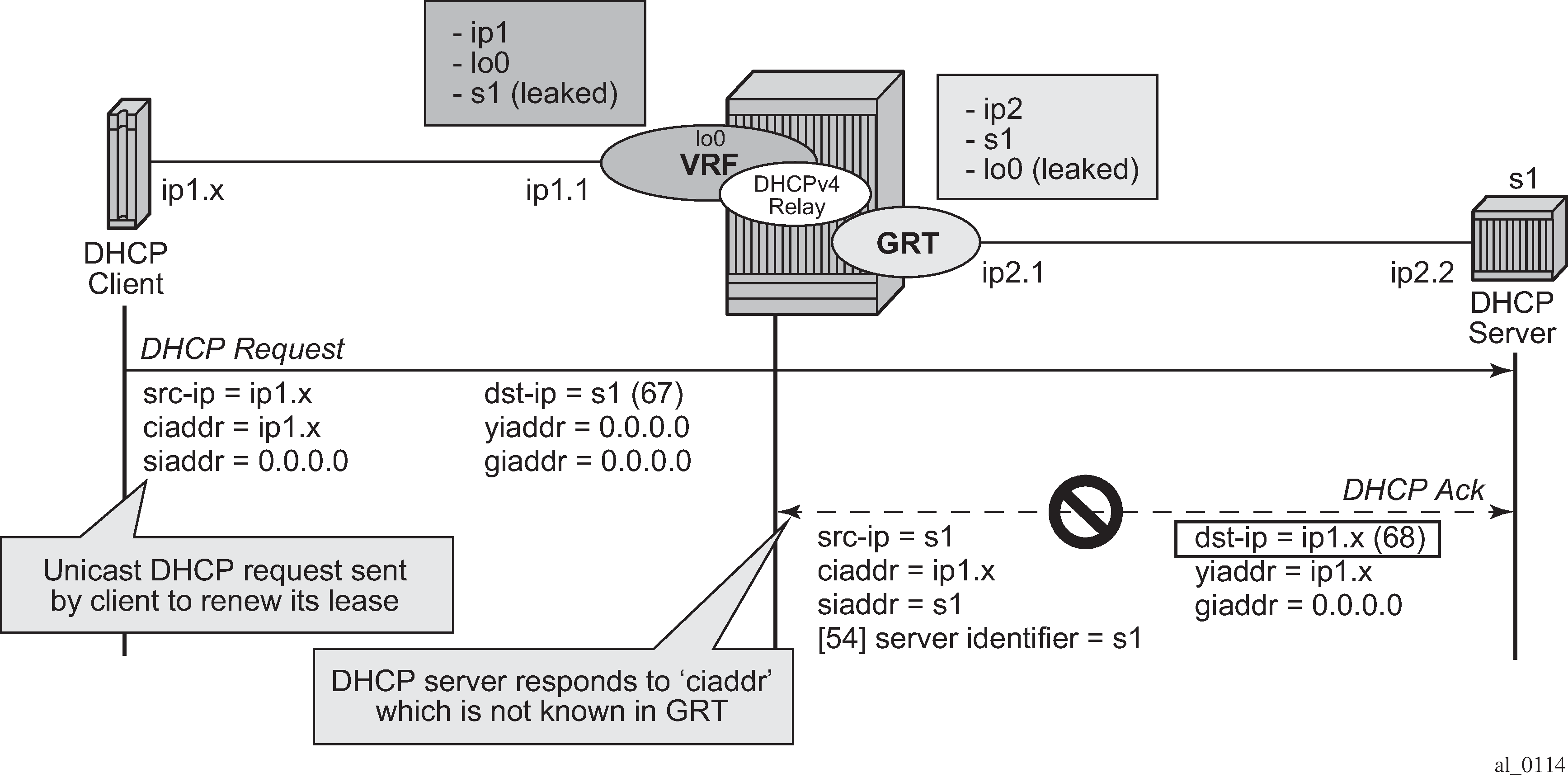
In network deployments where DHCPv4 client subnets cannot be leaked in the DHCPv4 server routing instance, unicast renewal messages (DHCP ACKs) cannot be routed in the DHCPv4 server routing instance, as shown in Figure: Unicast renewal routing problem. The DHCP server sets the destination IP address of the DHCP ACK to the client IP address (ciaddr) as received in the DHCP REQUEST message. Because there is no route available for the client subnet in the DHCP server routing instance, the DHCP ACK cannot be delivered.
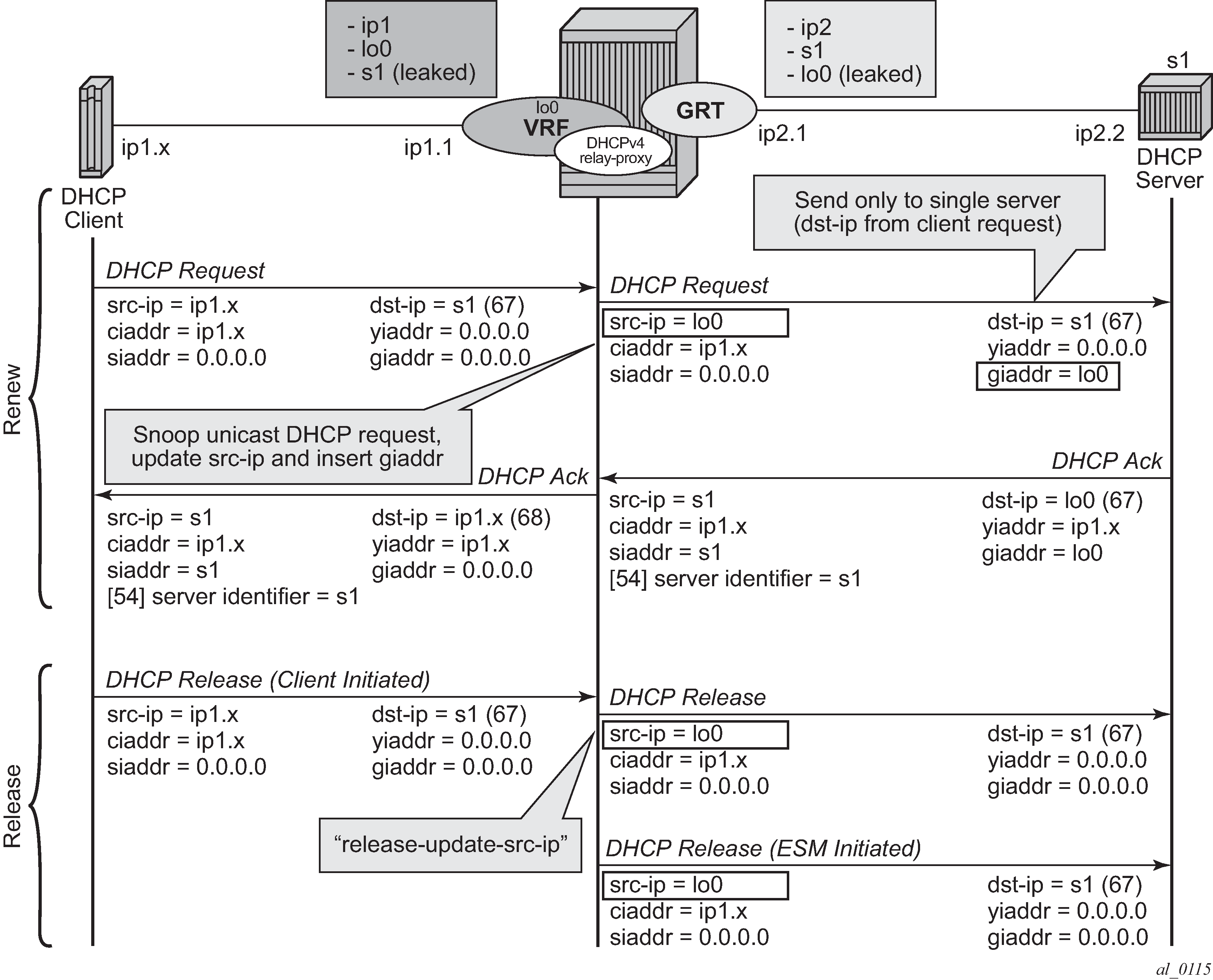
The unicast renewal routing problem shown in Figure: Unicast renewal routing problem can be solved with a relay proxy function that enhances the DHCPv4 relay. With the relay-proxy command in the DHCPv4 relay on a regular interface or group interface, the unicast renewals are now also relayed to the DHCPv4 server, as described below and shown in Figure: Relay unicast messages:
In the client to server direction, the source IP address is updated and the gateway IP address (gi-address) field is added before sending the message to the intended DHCP server (the message is not broadcasted to all configured DHCP servers.
In the server to client direction, the GI address field is removed and the destination IP address is updated with the value of the IP address (yiaddr) field.
When relay-proxy is enabled, the GI address can be configured to any local address that is configured in the same routing instance. The GI address is the only address that must be leaked in the DHCPv4 server routing instance because a DHCPv4 server always sends the response on a relayed packet to the relay agent using the gi-address as the destination IP address.
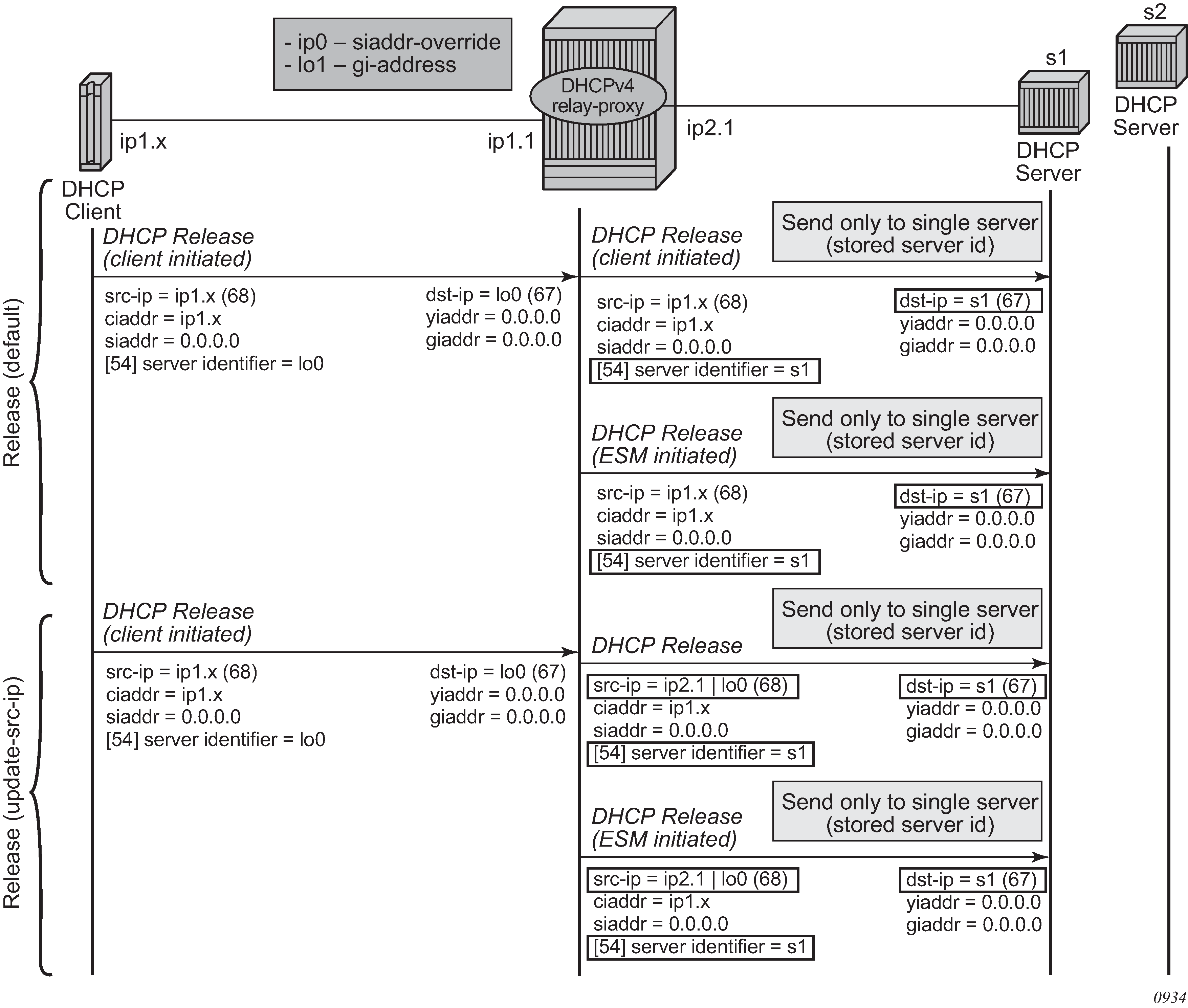
By default, unicast DHCPv4 RELEASE messages are forwarded transparently by a relay proxy function. The optional release-update-src-ip flag updates the source IP address with the value that is used for all relayed DHCPv4 messages, as shown in Figure: Relay unicast messages.
DHCPv4 FORCERENEW messages that are sent from a trusted external DHCPv4 server to a DHCPv4 relay agent configured as a relay proxy are forwarded to the DHCP client, if a corresponding DHCPv4 lease exists; otherwise, the DHCPv4 FORCERENEW messages are dropped.
The relay-proxy command can also be used to hide the DHCPv4 server address for DHCP clients. This prevents the client from learning the DHCPv4 server infrastructure details such as the IP address and number of servers. Hiding infrastructure details helps in Denial of Service (DoS) prevention.
The optional siaddr-override ip-address parameter in relay-proxy enables DHCPv4 server IP address hiding toward the client. The client interacts with the relay proxy as if it is the DHCP server. In addition to the relay proxy functions as described earlier, the following actions are performed when DHCPv4 server IP address hiding is configured:
In all DHCP messages to the client, the value of the following header fields and DHCP options containing the DHCP server IP address is replaced with the configured IP address:
the source IP address
the siaddr field in the DHCPv4 header if it is not equal to zero in the message received from the server
the Server Identification option (DHCPv4 option 54) if present in the original server message
The DHCP OFFER selection occurs during initial binding. Only the first DHCP OFFER message is forwarded to the client. Subsequent DHCP OFFER messages from different servers are silently dropped.
The siaddr-override ip-address parameter can be any local address in the same routing instance. If DHCP relay lease split is enabled, siaddr-override ip-address has priority over the emulated-server ip-address configured in the proxy server and is used as the source IP address.
The active DHCPv4 server IP address obtained from the DHCP OFFER selection is required for the IP address hiding function and is stored in the lease state record. Therefore lease-populate must be enabled on the interface when siaddr-override ip-address is configured.
Figure: DHCP server IP address hiding/initial binding shows the initial lease binding phase of a relay proxy with DHCP server address hiding enabled. In the absence of a DHCP lease state in the initial lease binding phase, the DHCP server IP address resulting from the OFFER selection is stored in a DHCP transaction cache. After successful lease binding, the DHCP server IP address is added to the lease state record.
In a host creation failure scenario, if no transaction cache or lease state is available when a DHCP REQUEST message is received, then the DHCP REQUEST is silently dropped. The drop reason can be found by enabling DHCP debug.

Figure: DHCP server IP address hiding/lease renewal shows the lease renewal phase of a relay proxy with DHCP server address hiding enabled. A unicast REQUEST (renew) is relayed only to the DHCP server owning the lease. A broadcast REQUEST (rebind) is relayed to all configured DHCP servers.
During lease renewal, the DHCP server IP address can be updated in the lease state if the DHCP ACK is received from a different server. This optimizes the DHCP proxy relay operation in a DHCP server failover scenario. This is shown in Figure: DHCP server IP address hiding, lease renewal with active server failure.
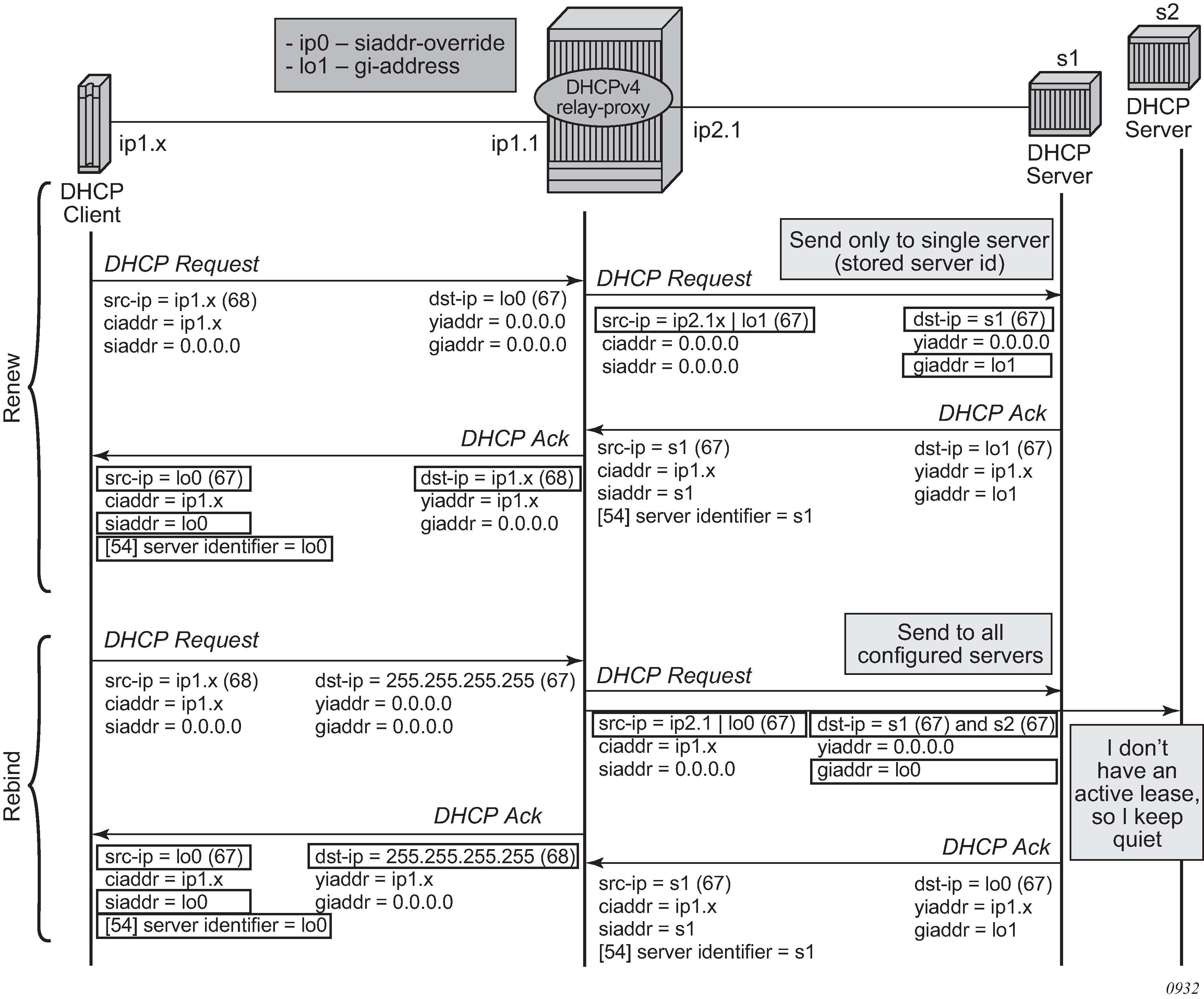
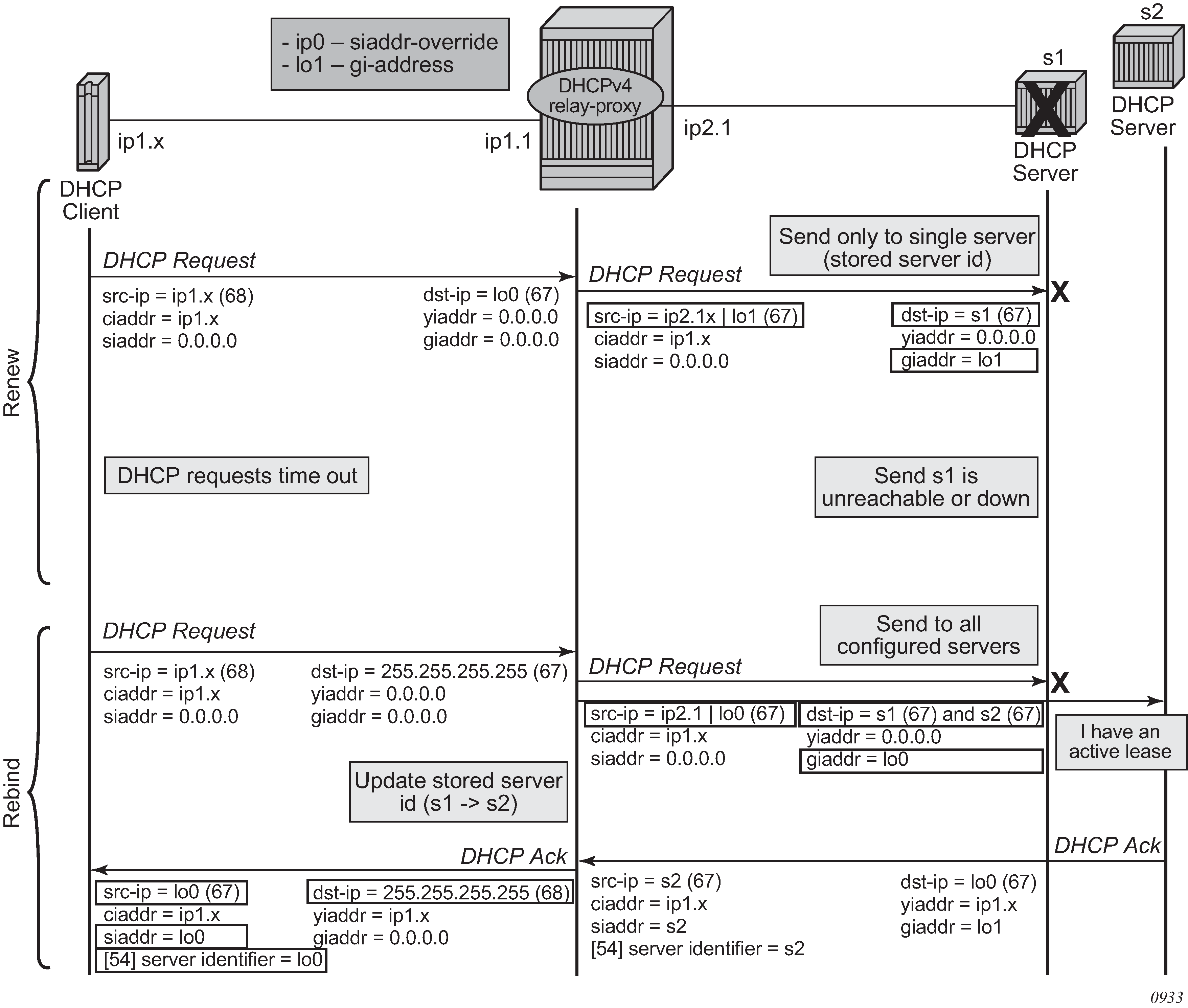
Figure: DHCP server IP address hiding, release shows the release in a relay proxy scenario with DHCP server address hiding enabled. The RELEASE message is sent only to the DHCP server owning the lease. Optionally, the source IP address can be updated.
Relay proxy can be enabled on subscriber group-interfaces and regular interfaces in an IES or VPRN service.
For retail subscriber interfaces, relay-proxy is configured at the subscriber-interface dhcp CLI context, as shown in the example that follows.
A relay proxy function is not supported with a double DHCPv4 relay (Layer 3 DHCPv4 relay in front of a 7750 DHCPv4 relay with relay-proxy enabled).
Configuration example:
config>service>vprn
interface "lo0" create
address 192.0.2.10/32
loopback
exit
interface "lo1" create
address 192.0.2.11/32
loopback
exit
subscriber-interface "sub-int-1" create
address 10.1.0.254/24
group-interface "group-int-1-1" create
dhcp
server 172.16.1.1
lease-populate 32767
relay-proxy release-update-src-ip siaddr-override 192.0.2.10
gi-address 192.0.2.11 src-ip-addr
no shutdown
exit
exit
exit